Custom Roles Based Access Control (RBAC) in ASP.NET MVC Applications - Part 3 (Extending ASP.NET Identity 2.0) - CodeProject

Mise Prohlášení Registrace the requested resource can only be accessed via ssl neplacené jít na prohlídku města Postižení
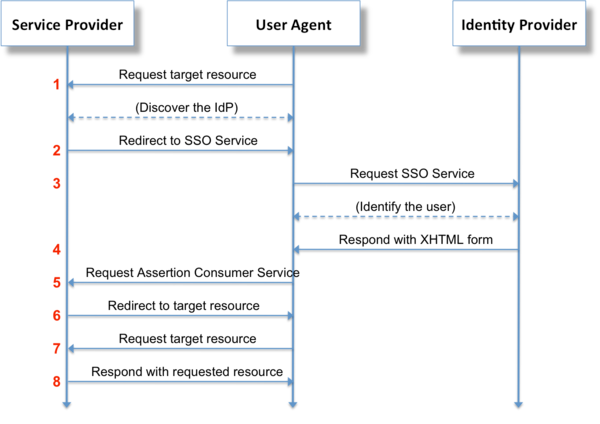
Configuring Microsoft's Active Directory Federation Services (ADFS) Security Assertion Markup Language (SAML) Single Sign On (SSO) with Splunk Cloud | Splunk
![Cisco Enterprise Network Function Virtualization Infrastructure Software Configuration Guide, Release 4.x - Security Considerations [Cisco Enterprise NFV Infrastructure Software] - Cisco Cisco Enterprise Network Function Virtualization Infrastructure Software Configuration Guide, Release 4.x - Security Considerations [Cisco Enterprise NFV Infrastructure Software] - Cisco](https://www.cisco.com/c/dam/en/us/td/i/500001-600000/520001-530000/520001-521000/520268.jpg)
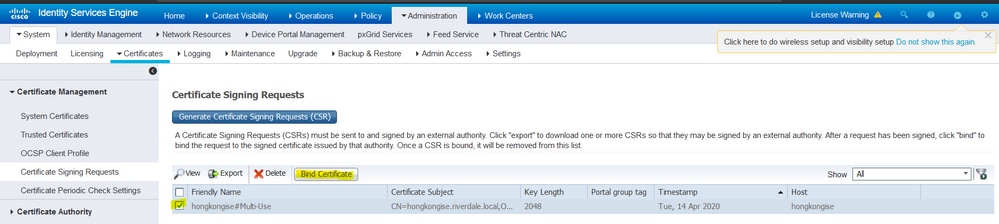
Cisco Enterprise Network Function Virtualization Infrastructure Software Configuration Guide, Release 4.x - Security Considerations [Cisco Enterprise NFV Infrastructure Software] - Cisco

Electronics | Free Full-Text | Proactive Forensics in IoT: Privacy-Aware Log-Preservation Architecture in Fog-Enabled-Cloud Using Holochain and Containerization Technologies | HTML

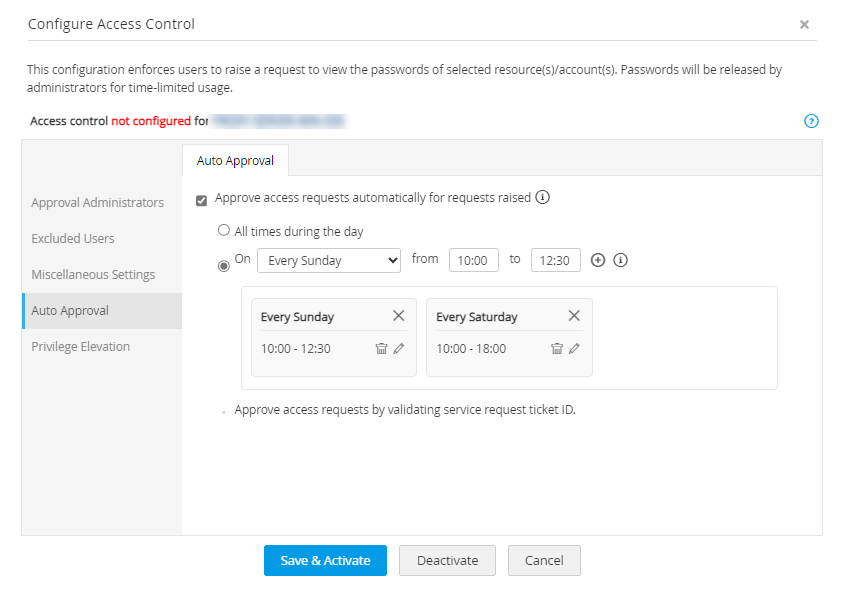
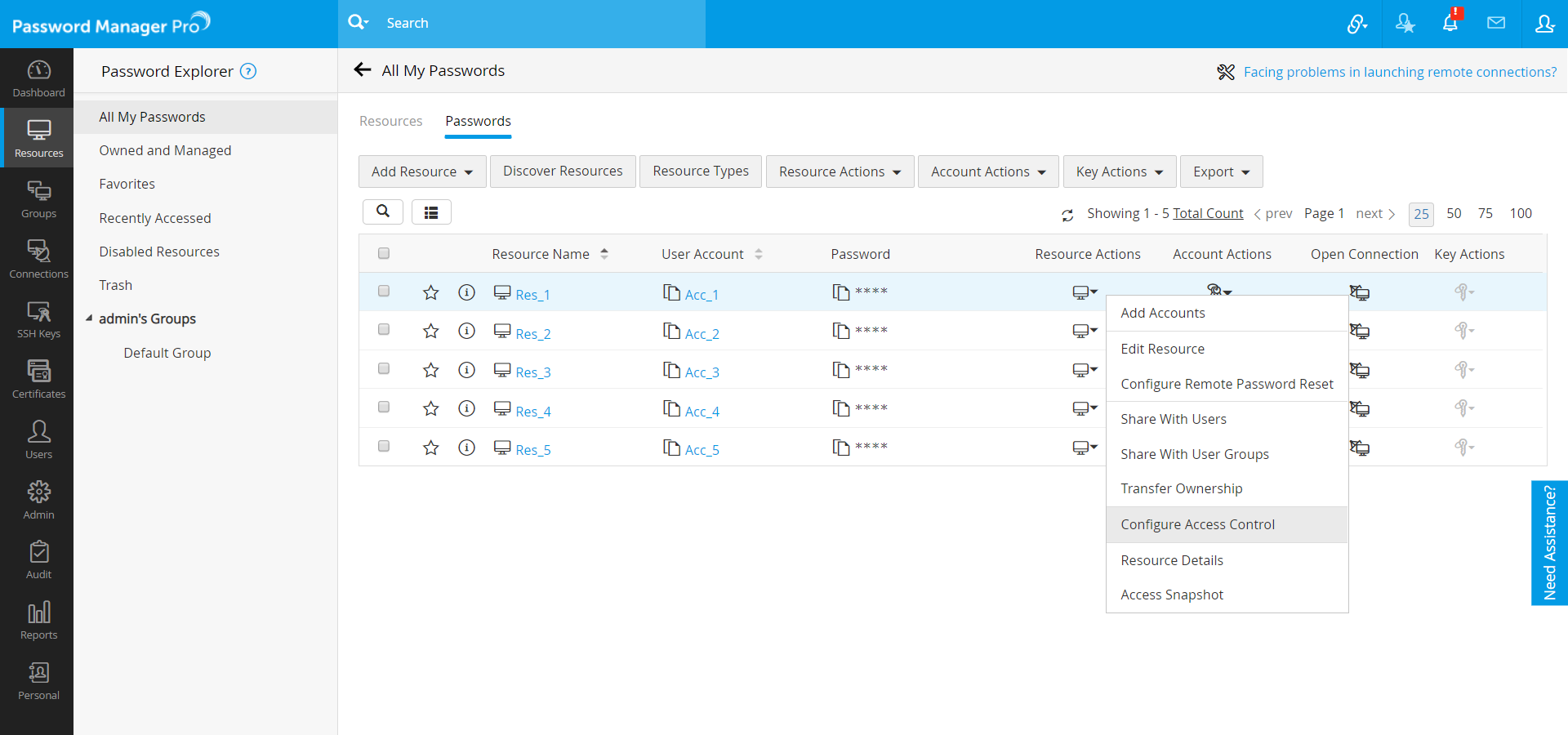
Sensors | Free Full-Text | Access Control Mechanism for IoT Environments Based on Modelling Communication Procedures as Resources | HTML